SSH shell
This article describes server behavior when a client connects to the server using an SSH client (e.g., PuTTY) and related configuration options.
SSH shell modes
The server supports three modes of behavior for SSH shell.
These can be configured in the configuration file, using web administration, or (per user) using the burusftp user update command.
none
Minimal shell with SCP will be available. File system access will be restricted to the user’s path mapping. This is the default option.
terminal 2.5.0+
A shell process (e.g., cmd.exe, PowerShell) will be spawned. Users are not restricted to their path mappings when using the shell.
legacy
Same as none, with SSH aliases support.
DEPRECATED
Legacy mode is marked as deprecated and most likely will be removed in future versions of Buru SFTP Server.SSH terminal mode 2.5.0+
Clients may use SSH to connect to their favorite shell (cmd.exe, PowerShell, bash, etc.), with a similar experience to connecting to a Linux machine. The shell executable and home directory can be configured globally with the possibility of per-user override.
The shell process runs under the service user account, unless the user has Windows impersonation enabled (in which case it uses the associated Windows account).
Clients connected using SSH bypass path mappings and gain access to the whole file system, with restrictions imposed only by the operating system for the service (or impersonated) user.
This is especially dangerous when the service runs under a privileged user account.
Use this mode only if you know what you are doing.
To run the terminal shell as a different Windows user, the service account must have the “Replace a process level token” (SeAssignPrimaryTokenPrivilege) and “Adjust memory quotas for a process” (SeIncreaseQuotaPrivilege) privileges. The SYSTEM account has these by default; a custom service account must have them explicitly granted.
Terminal mode relies on Windows’ ConPTY API, which is available only on new platforms: Windows 10 version 1809 and newer, Windows Server 2019 and newer. Impersonation is available in Pro edition only.
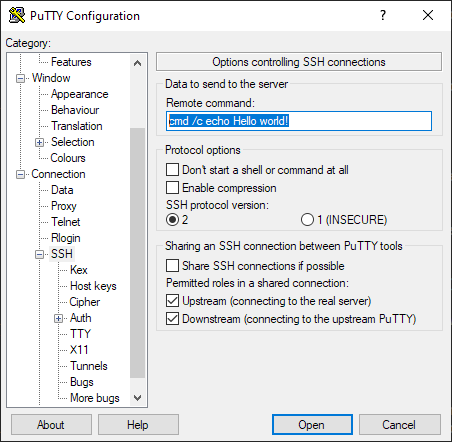
SSH exec
Clients may ask to execute a command directly using the SSH ’exec’ command (overriding the default shell), which is useful for executing commands that do not require a shell session.
Putty example configuration:
Feedback
Was this page helpful?
Glad to hear it! Please tell us how we can improve.
Sorry to hear that. Please tell us how we can improve.